- Home
- Services
- Hi-Line Engineering
- About
- Careers
- Contact
- Requests For Proposals
ENHANCING PHYSICAL SECURITY FOR CRITICAL ELECTRIC SYSTEM FACILITIES
by GDS Associates, Inc | July 17, 2023 |
 In the electric utility industry, we have spent recent years focusing on cyber threats against our facilities, but now physical threats seem to be making a comeback. Many electric utilities have spent large amounts of money developing and deploying cyber security protections at their critical facilities, including control centers and major substations. Some of the utilities have also focused on increasing their physical security controls, but that has not been the major push from FERC and NERC until recently and, even then, only for the major high voltage substations and control centers (NERC CIP-014). Most companies use standard physical security deterrents that are good enough to meet the minimum requirements for compliance and safety, which may not be good enough in the new physical security threat landscape that we are now facing. Some examples of the changing physical threat landscape are shown in the ongoing war in Ukraine and the substation attacks in North Carolina.
In the electric utility industry, we have spent recent years focusing on cyber threats against our facilities, but now physical threats seem to be making a comeback. Many electric utilities have spent large amounts of money developing and deploying cyber security protections at their critical facilities, including control centers and major substations. Some of the utilities have also focused on increasing their physical security controls, but that has not been the major push from FERC and NERC until recently and, even then, only for the major high voltage substations and control centers (NERC CIP-014). Most companies use standard physical security deterrents that are good enough to meet the minimum requirements for compliance and safety, which may not be good enough in the new physical security threat landscape that we are now facing. Some examples of the changing physical threat landscape are shown in the ongoing war in Ukraine and the substation attacks in North Carolina.
On the international front, Russia has been attempting to destabilize Ukraine for years, by using cyber-attacks against the power grid. Since the start of the war, the Russian forces are actively attacking the Ukraine power grid using both cyber and physical methods. The news headlines show how many articles there are about Ukraine’s struggles to keep the lights on from Russia’s constant attacks. Domestically, in North Carolina, extremists targeted multiple substations and other power facilities with physical attacks in an attempt to cause major blackouts and potentially create a panic in the area. We have
also seen similar tactics used for physical attacks on electric system facilities in Oregon and Washington. Attacking the electric grid is often seen as one of the easiest ways for an adversary to destabilize a country.
 When compared to cyber security, physical security encompasses a different thought process. In cyber security, the overall goal is to prevent cyber-attacks and to be able to restore that cyber asset after a critical failure, but for physical security, the main goal is to delay the attacker’s ability to compromise your facility long enough for law enforcement to respond and stop the attack. In physical security controls, the focus is on delaying the ability to access or compromise the critical facility as long as needed and not necessarily on stopping or preventing an attack. That being said, good physical security controls can be a preventive measure to discourage would-be attackers.
When compared to cyber security, physical security encompasses a different thought process. In cyber security, the overall goal is to prevent cyber-attacks and to be able to restore that cyber asset after a critical failure, but for physical security, the main goal is to delay the attacker’s ability to compromise your facility long enough for law enforcement to respond and stop the attack. In physical security controls, the focus is on delaying the ability to access or compromise the critical facility as long as needed and not necessarily on stopping or preventing an attack. That being said, good physical security controls can be a preventive measure to discourage would-be attackers.
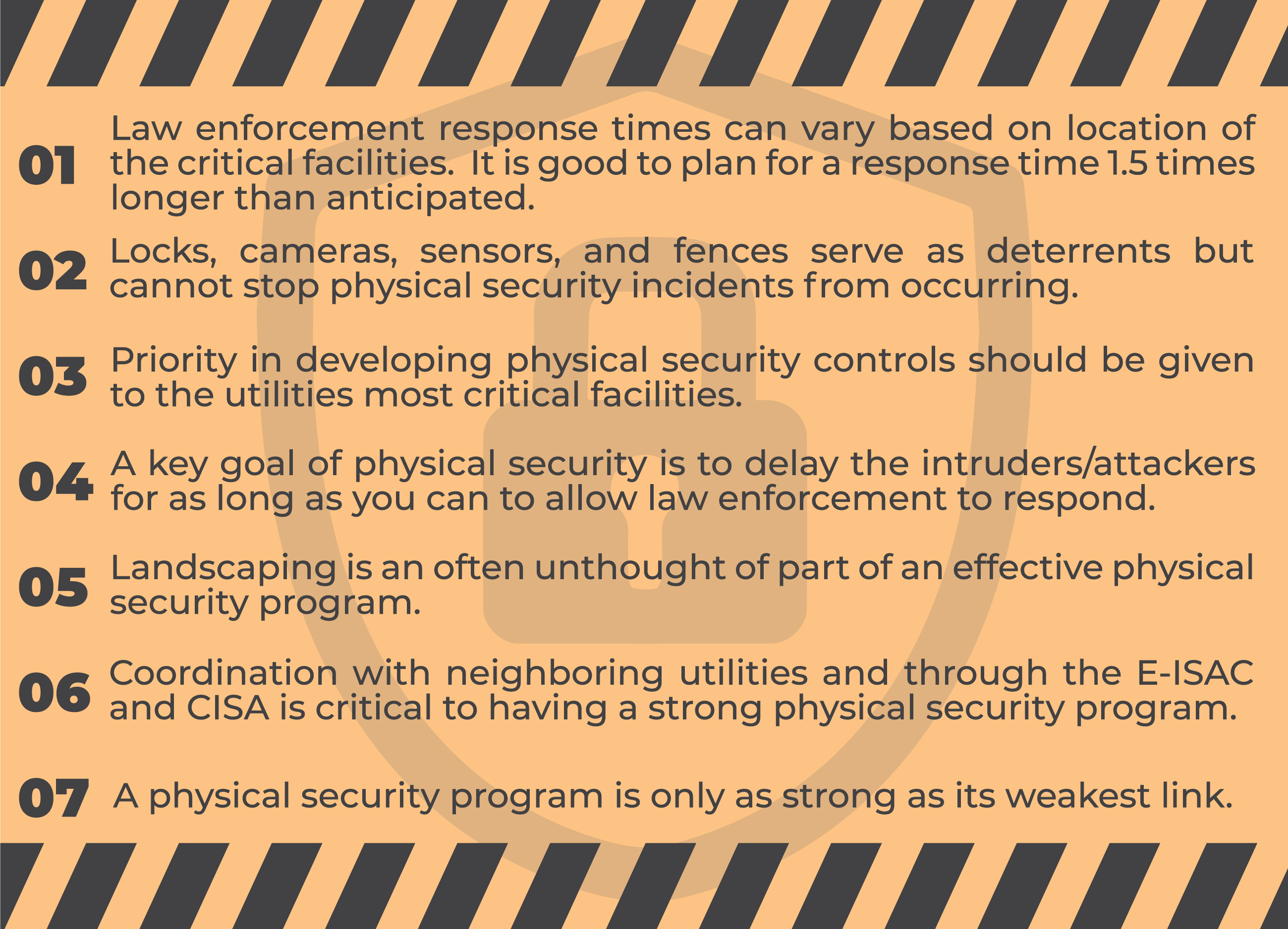
For many, when we think of physical security, we think of locks on doors, fences, sensors, or security cameras, but there are many more facets to a strong physical security program.
Facility design and landscaping can both be key components of physical security. For example, if you build a server room that is critical for your organization and you deploy a Physical Access Control System (PACS), the room seems to be physically secure, but if the walls of the room are made of only sheetrock, the PACS will not provide adequate security. Some physical security experts conduct what is called the kick test, if the expert can kick a hole in the wall, they fail the test. Attackers could simply break through the wall with little effort and access the room without even needing to touch the door. One way to prevent this physical security weakness is by adding additional wall protection, such as steel mesh or ballistic paneling. In many cases, physical security is not considered during the initial design process of a facility and then the utility is forced to make modifications to a critical facility to add new physical security controls. The post construction modification can be very costly and, in many cases, would have been much more economical and efficient if they were considered during the design phase.
When devising a physical security program, the designer should consider the facility location, the law enforcement response time, and the criticality of that facility. A remote critical facility may seem to be at a lower risk for a physical attack, but the law enforcement response time may be much longer than for a facility that is in a city. Physical security experts recommend that you take into consideration the average response time of law enforcement may be roughly 1.5 times greater than anticipated, especially if the facility is in a remote location. For example, if you have a major substation located inside the city limits, the law enforcement response time may within 30 minutes of receiving the notification of an event, but if that substation is located in a rural part of the county the repones time maybe hours and not minutes.
 Utilities should coordinate with local law enforcement to assess realistic response times to their critical facilities. If you have a critical facility that has a 30-minute response time for local law enforcement, building in at least 30 minutes of delays is crucial. Coordination with local law enforcement is vital to ensure all parties understand the level of importance for physical security as well as understanding the proper way to respond to an event at the facility. This may include training for the law enforcement partners on how to safely access and respond to physical attacks at dangerous high voltage facilities, such as Bulk Electric System substations.
Utilities should coordinate with local law enforcement to assess realistic response times to their critical facilities. If you have a critical facility that has a 30-minute response time for local law enforcement, building in at least 30 minutes of delays is crucial. Coordination with local law enforcement is vital to ensure all parties understand the level of importance for physical security as well as understanding the proper way to respond to an event at the facility. This may include training for the law enforcement partners on how to safely access and respond to physical attacks at dangerous high voltage facilities, such as Bulk Electric System substations.
In addition to potentially delayed law enforcement response times, there are other easily identified weak points in most substation physical security controls. The first control that can be a weak point is the substation fence. Most facilities us a standard fence of 2-inch links with 9-gauge wire it which meets the minimum requirements for a safety and security but can easily be cut through in less than a minute. If the substation uses thicker gauge wire and a smaller link, such as a 6-gauge and 5/8-inch link, the delay in cutting through the fence can be increased by 6 minutes. Those 6 minutes could be vital to maintain the integrity of that facility and add more time for law enforcement to respond.
A second physical security control that can be a weak point is the locks that are used on the facility gates. Unfortunately, most standard pad and door locks are not very secure. The standard padlock that is commonly used throughout the United States can be compromised by anyone who has watched a YouTube video and spent 30 minutes learning how to lock pick. Many standard locks can also be broken or cut though. The best option for critical facilities is to use high security locks with pick resistant pins or a digital signature, such as smart locks. The high security locks can slow down an attacker and provide for more time for a law enforcement response.
A third control that can be both an enhancement and a determent to the physical security of a critical facility is landscaping. If utilized properly, landscaping can both add security controls to the facility and make the facility look aesthetically pleasing. For example, hard to walk on boulders or spikes around the facility will slow down a potential attacker and allow more time for the law enforcement response. Strategically planted bushes can be used to hinder line of sight attacks by gunfire. Landscaping can also be a problem for physical security as it can allow attackers to hide and avoid security cameras or even provide an easier way to climb a fence and enter the facility if it is not well maintained. Clearing trees and brush from around a facility removes the possibility of an attacker using the brush as cover or a method of breaching the physical security perimeter.
A key component to a good physical security program is coordination with neighboring utilities to jointly protect and monitor for security events at critical facilities. The neighboring utilities’ security controls also matter to your utility for multiple reasons: 1) electric utilities are part of the interconnected electric grid and damage to a neighbors’ facility may also cause outages for your customers; 2) many utilities have shared facilities and want to ensure that both entities have equally as strong security controls; and 3) strong coordinated physical security controls can help deter attackers from either entities’ critical facilities. The electric utility industry needs to continue to have conversations between entities about security events that have happened, the responses to those events, and security measures that they put into place to deter future events. Having industry wide transparency of threats and events allows for a better picture of what is happening in the broader scope. For example, there could be a pattern of multiple security events that was not noticed until all the information from multiple entities is gathered and analyzed.
A good way to stay knowledgeable about both physical and cyber security threats to the electric industry is through participation in the North American Energy Reliability Corporation (NERC) and Department of Energy (DOE) Electricity Information Sharing and Analysis Center (E-ISAC). The E-ISAC is open to all electric utilities and provides a secured platform form sharing information regarding potential and actual physical and cyber security events. Water and gas utilities have similar Information Sharing and Analysis Centers. The Department of Homeland Security launched the Cyber and Infrastructure Security Agency (CISA) in 2018 to assist critical infrastructure entities in protecting their facilities and systems. All of these industry and government groups provide information on ways to protect your entity from physical and cyber security threats and ways to coordinate with fellow utilities as well as local, state, and federal law enforcement entities.
To summarize, here are some key take aways that will be helpful in deploying an effective physical security program:
Enhanced physical security of your facilities not only protects you and your customers from potentially long outages but also helps take steps to secure the overall North American interconnected electric grid. In many cases the investments that are made for physical security enhancements to protect transmission facilities can be recovered through your Transmission Tariff or your Regional Transmission Organization (RTO) Tariff. Additional security enhancements on the critical facilities on the interconnected electric system are a win for all parties involved.
 For more information or to comment on this
For more information or to comment on this
article, please contact:
Dex Underwood, Analyst
GDS Associates, Inc. - Marietta, GA
770-799-2395
dex.underwood@gdsassociates.com
GET OUR NEWSLETTER
RECENT POSTS
- Protect the Grid: Act on Facility Ratings Today
- Why MOD-026-2 Matters: Raising the Bar for Generator and IBR Modeling Reliability
- Exploring the 2026-2028 Reliability Standards Development Plan
- Blackstart Resource Availability During Extreme Cold Weather Conditions
- DOE Pushes FERC to Accelerate Large Load Grid Access
Archives
- December 2015 (8)
- June 2025 (7)
- January 2016 (6)
- July 2016 (6)
- March 2021 (6)
- May 2022 (6)
- August 2020 (5)
- March 2015 (4)
- January 2019 (4)
- June 2019 (4)
- August 2019 (4)
- February 2020 (4)
- May 2020 (4)
- June 2020 (4)
- December 2020 (4)
- July 2021 (4)
- October 2021 (4)
- April 2024 (4)
- December 2024 (4)
- May 2025 (4)
- April 2015 (3)
- August 2016 (3)
- February 2017 (3)
- July 2017 (3)
- February 2018 (3)
- February 2019 (3)
- November 2019 (3)
- March 2020 (3)
- April 2020 (3)
- September 2021 (3)
- December 2021 (3)
- August 2022 (3)
- December 2022 (3)
- April 2023 (3)
- July 2023 (3)
- December 2023 (3)
- September 2024 (3)
- October 2025 (3)
- December 2025 (3)
- May 2014 (2)
- February 2016 (2)
- March 2016 (2)
- September 2016 (2)
- November 2016 (2)
- January 2017 (2)
- July 2018 (2)
- November 2018 (2)
- March 2019 (2)
- May 2019 (2)
- July 2020 (2)
- September 2020 (2)
- April 2021 (2)
- August 2021 (2)
- October 2024 (2)
- September 2025 (2)
- February 2014 (1)
- April 2014 (1)
- July 2014 (1)
- August 2014 (1)
- November 2014 (1)
- February 2015 (1)
- May 2015 (1)
- June 2015 (1)
- November 2015 (1)
- October 2016 (1)
- December 2016 (1)
- October 2018 (1)
- December 2018 (1)
- April 2019 (1)
- July 2019 (1)
- September 2019 (1)
- October 2020 (1)
- November 2020 (1)
- February 2021 (1)
- April 2022 (1)
- July 2022 (1)
- October 2022 (1)
- August 2023 (1)
- October 2023 (1)
- July 2025 (1)
- November 2025 (1)
- January 2026 (1)
Categories
- Newsletter - TransActions (85)
- News (78)
- Employee Spotlight (35)
- Energy Use & Efficiency (28)
- Energy, Reliability, and Security (18)
- Other Specialized Services (11)
- Environment & Safety (10)
- Power Supply (8)
- Transmission (8)
- NERC (7)
- Utility Rates (7)
- Cyber Security (5)
- Energy Supply (4)
- Hi-Line: Utility Distribution Services (4)
- Battery Energy Storage (3)
- Uncategorized (2)
- Agriculture (1)
- Hi-Line: Seminars & Testing (1)